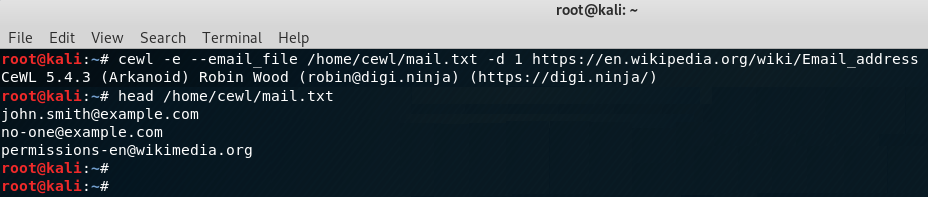
Have you just created your first Azure VM and are looking for a good, secure way to connect to you new machine without exposing more than necessary to the internet? Maybe you just want to run a few machines and don’t want to spend money on firewalls to configure VPN to your Azure Virtual Network (VNET)?
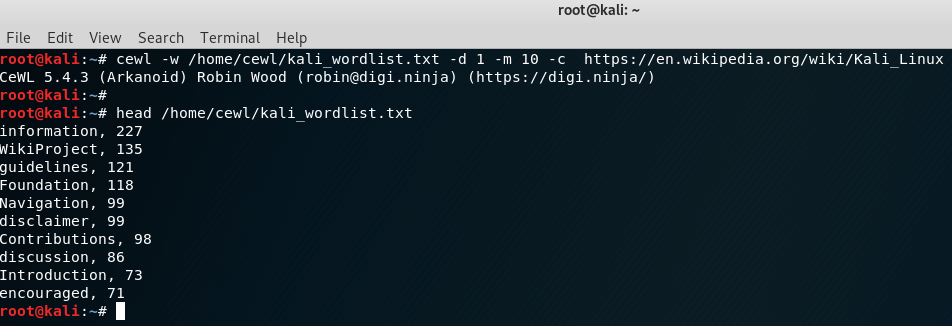
In this post I will explain a method that can be used to connect to your machine securely without any cost. After reading this post you will know how you can set up a SSH tunnel to your machine so you only need to expose TCP port 22 to the internet. I will also show you how you can limit the access to that port by configuring a Network Security Group (NSG) in Microsoft Azure to only allow your own IP to connect. You will connect to the VM using Putty and either Google Chrome or Mozilla Firefox. We start off by configuring the NSG in Azure.
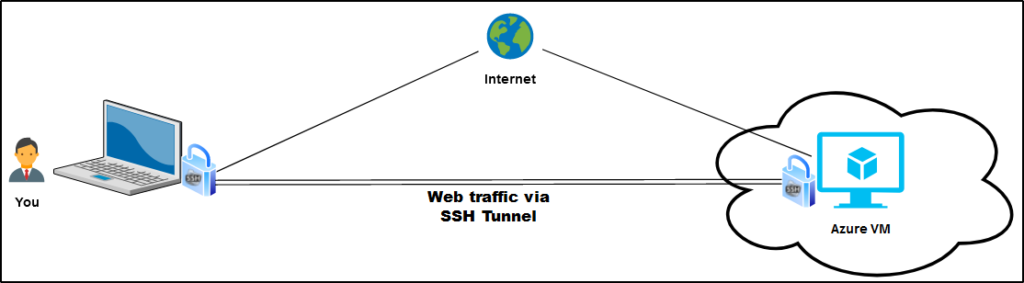
Configuring NSG in Azure:
The first thing that we need to do is to allow you to SSH to your machine and we do that by configuring the NSG. You want to modify the inbound security rule named ‘default-allow-ssh’ and you do that by clicking on ‘Inbound security rules’ in the left menu.
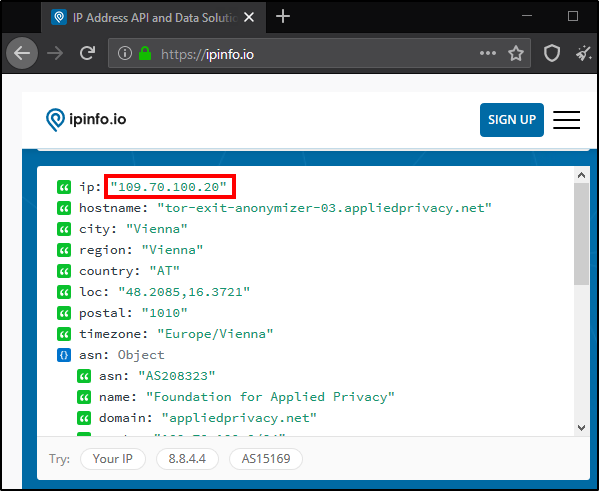
You should now add your public IP to the rule to allow you to connect from your home network. You probably know how to get your public IP but if you don’t know, one simple way is by visiting https://ipinfo.io and copy the address from there.
When you have the IP ready, click on the ‘default-allow-ssh’-rule to expand it and then add your IP to ‘Source IP addresses/CIDR ranges’ and press ‘Save’.
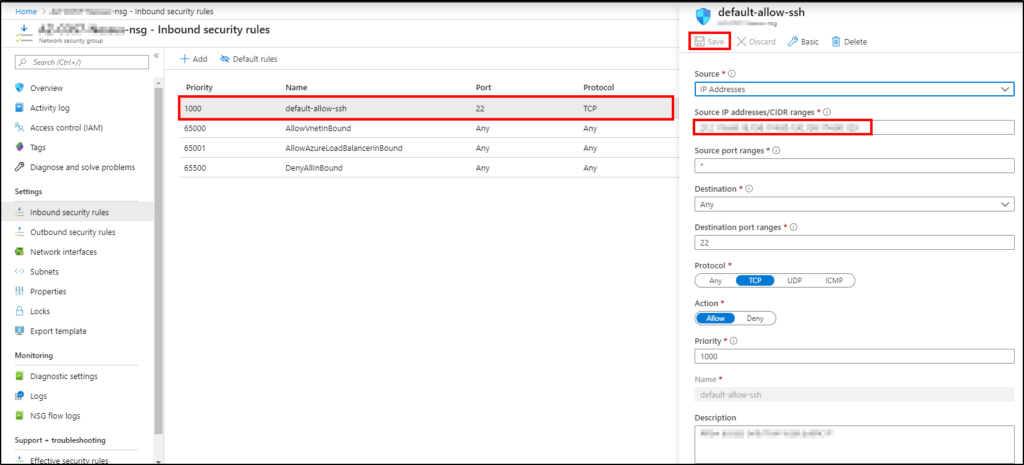
The Azure configuration is now done. Lets move on to the Putty configuration.
Configuring Putty:
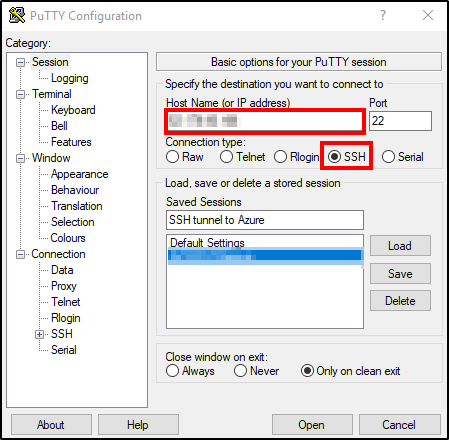
If you don’t have Putty installed you can download it from the official website and then just install it. After you have installed the software the first step is to run Putty and add the public IP of your Azure VM and select SSH port 22.
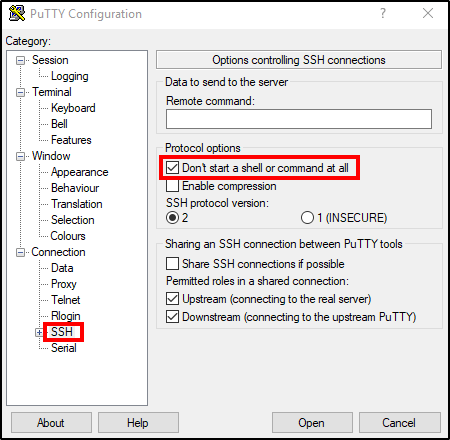
Then navigate to SSH and check ‘Don’t start a shell or command at all’.
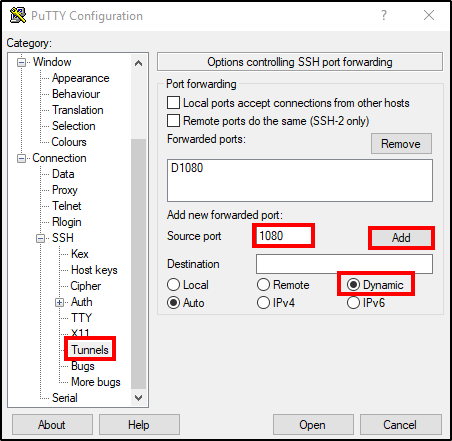
Move on by expanding SSH (+) and go to Tunnels. Add a forwarded port by choosing ‘Source port’. In this example we use port 1080. Select ‘Dynamic’ for destination and then press ‘Add’. Now you should see ‘D1080’ added above.
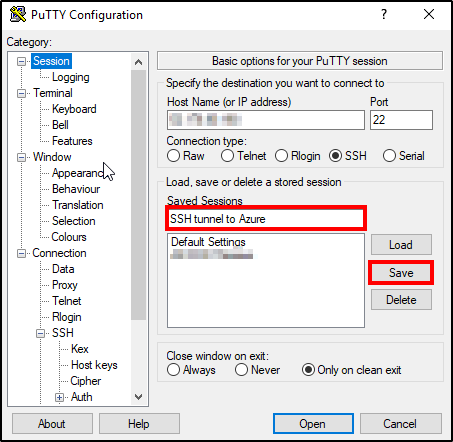
If you don’t want to configure these settings every time you want to use the tunnel you can save the session. That is done by going back to ‘Session’ and enter a name and then press ‘Save’.
Now the tunnel is ready and we just need to start it. Click on ‘Open’, enter your SSH credentials and press enter and the tunnel should be up and running.
Verify that the tunnel works:
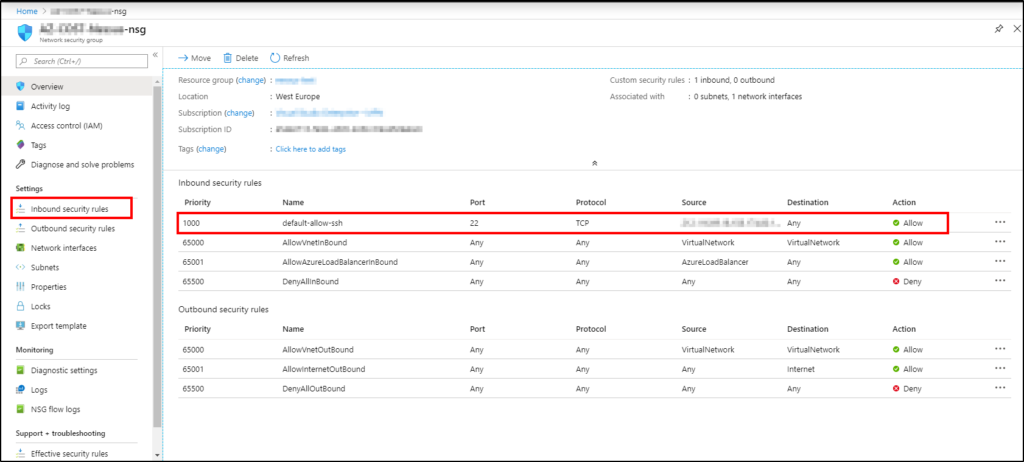
You will probably want to make sure that the tunnel works as expected and we can verify that by configuring a simple HTTP server on the VM. In this example CentOS7 was used but it can be done on most machines.
Step one is to open another putty window and connect to you VM via SSH. Navigate to your home folder (cd /home) and create a directory (mkdir testfolder). Cd into that folder and create a testfile (touch text.txt). Then run the following command to run a python based HTTP-server on port 80.
sudo python -m SimpleHTTPServer 80Your server will now listen for incoming connections on port 80. But since you don’t allow any connections to port 80 in the NSG you won’t be able to go directly to port 80. We need to send our HTTP traffic in the SSH tunnel to be able to reach it and we do that by configuring proxy settings in our web browser. This can be done in most of the common browsers and I will show you how to do it in Firefox and Chrome.
Chrome:
To configure proxy for Chrome you just right click on Chrome in the task bar and select ‘Properties’. You then need to add some run parameters.
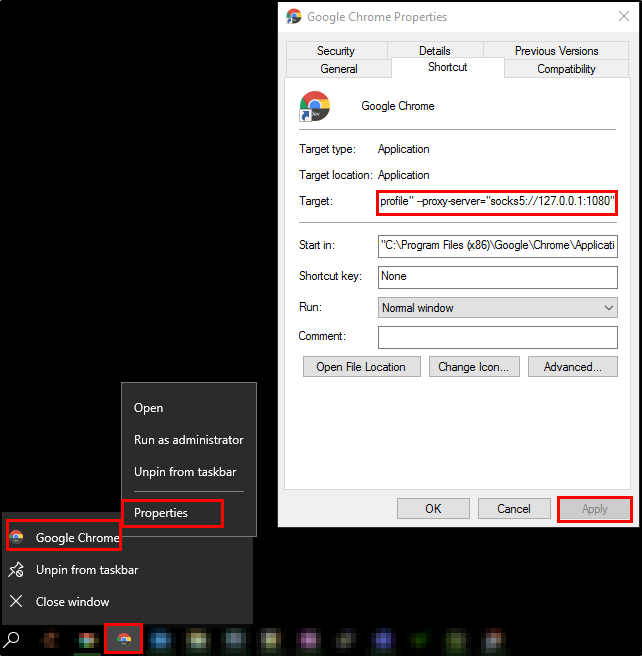
The parameters you should add are:
--user-data-dir="%USERPROFILE%\proxy-profile"
--proxy-server="socks5://127.0.0.1:1080"Firefox:
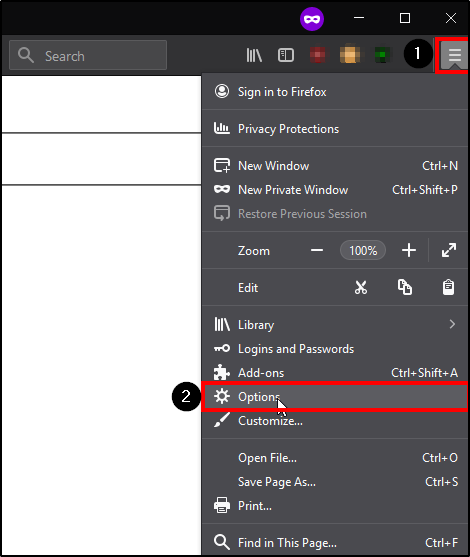
For Firefox you just open up the browser, open the menu (1) and click on ‘Options’ (2).
Then you search for proxy and click on ‘Settings’
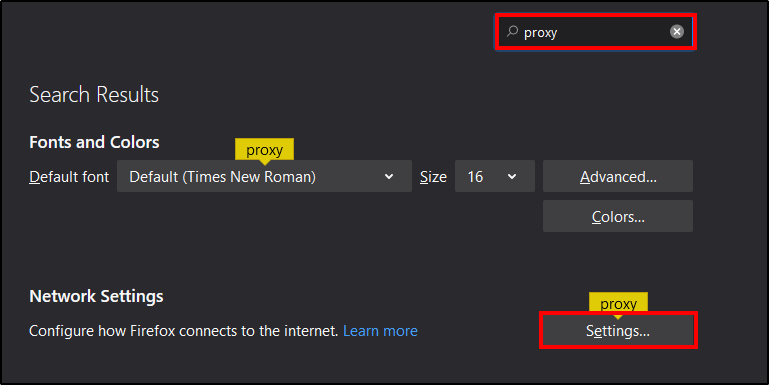
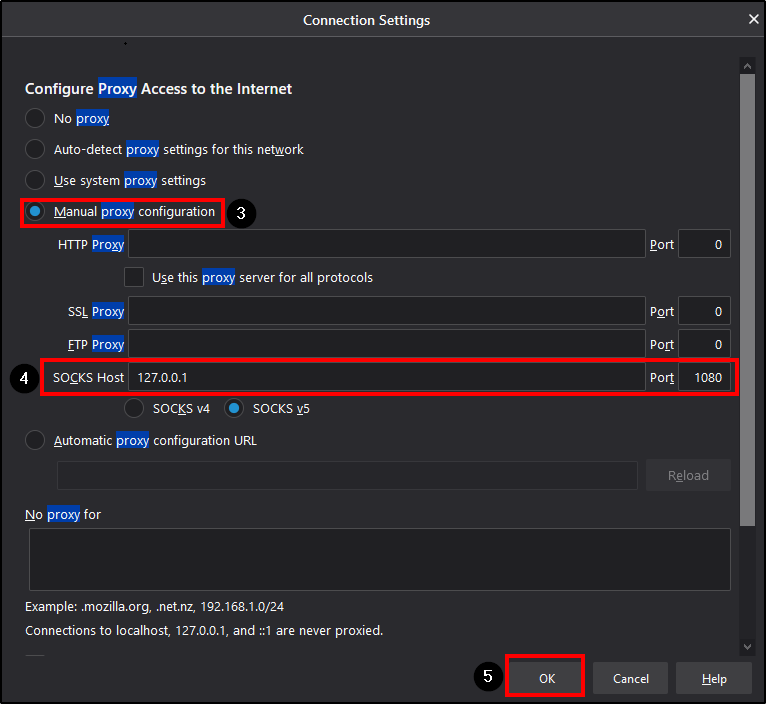
Select ‘Manual proxy configuration'(3) and then add ‘Socks Host 127.0.0.1 Port 1080′(4) and ‘SOCKS v5’ like in the example below.
After configuring the proxy settings you can just browse to the internal IP of your Azure VM. You can find the internal IP in the overview of the VM.
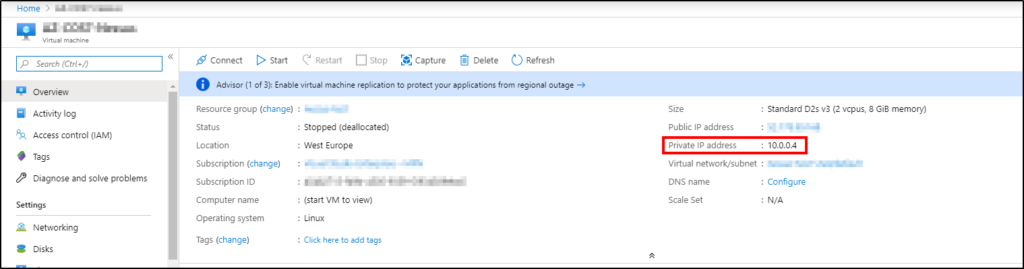
Then just browse to the IP ‘http://10.0.0.4’
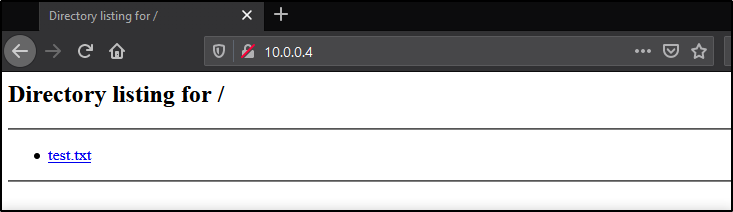
Voila, you should now see the test file (test.txt) that you created earlier.
I really hope you found this guide useful, if you have any questions or reflections please send me a message on twitter.
/Rickard