This post is about httprobe which is a tool for quickly probing for active http and https servers. If you have a list with subdomains you can quickly check which are active by using this tool. Httprobe is available on Github and the tool was created by Tom Hudson (@tomnomnom on Twitter).
Pre requisites:
1. You need to have Golang installed. If you haven’t used golang before and need help to get started, read my guide on how to install Golang on Kali Linux
2. Download ‘httprobe’ by running go get -u github.com/tomnomnom/httprobe
3. If you used my guide to install Go you can now find ‘httprobe’ at:/root/go-workspace/bin/assetfinder
Basic usage:
To use httprobe you need to print out your domains and pipe them to httprobe. In the example below we are are using cat to read the data from domains.txt and gives its content as output to httprobe.cat domains.txt | httprobe
Adding extra ports:
By default httprobe is probing for http on port 80 and https on port 443. We can add other ports by using the ‘-p’ parameter. cat domains.txt | httprobe -p http:8080 -p https:8443
Skip default ports and only probe for defined ports:
By adding ‘-s’ parameter the default ports will be ignored.
cat domains.txt | httprobe -s -p http:8080 -p https:8443
Specify a timeout:
If you know that the response time on the target server might be high you can specify a custom timeout by using the ‘-t’ parameter. The time is configured in milliseconds.
cat domains.txt | httprobe -t 10000
Combine with other tools:
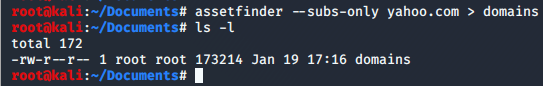
You can combine ‘httprobe’ with other tools such as ‘assetfinder’. If you don’t know about assetfinder you can read my earlier post that helps you getting started with assetfinder.
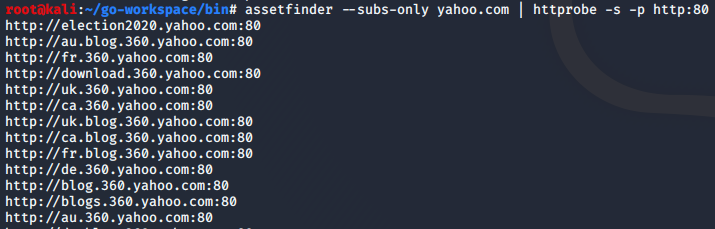
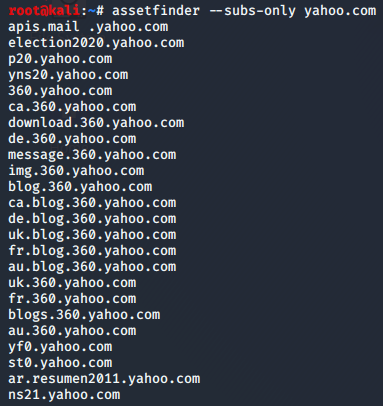
One example on how you can chain assetfinder with httprobe.
assetfinder --subs-only yahoo.com | httprobe -s -p http:80
In the example we first searched for subdomains at yahoo.com and piped the result to httprobe to find out which of the subdomains that were listening on port 80.