In this post I will describe how you can crack a KeePass Database file (.kdbx) in an easy way. Or to be correct we are not cracking the DB, we are cracking the password hash.
To demonstrate this I created a new database that I called “SecretDB.kdbx” and our mission will be to find out which master password I chose for the database.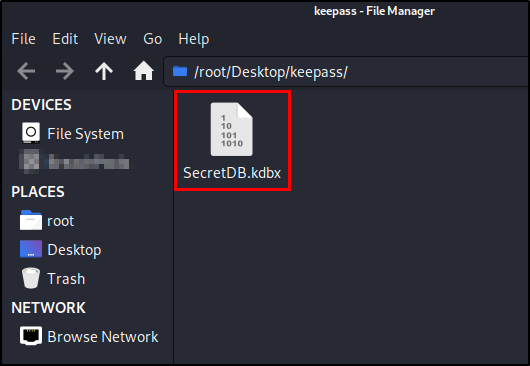
To be able to crack the hash we will need to extract and save it and that can be done with the John the ripper utility tool “keepass2john“. It comes with Kali Linux so you don’t have to install it.
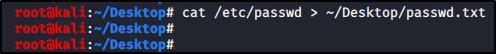
What you do to extract the hash is really simple, you just run:
keepass2john SecretDB.kdbx
You can also send the output to a file by adding “>” like I did in the screenshot below.keepass2john SecretDB.kdbx > Keepasshash.txt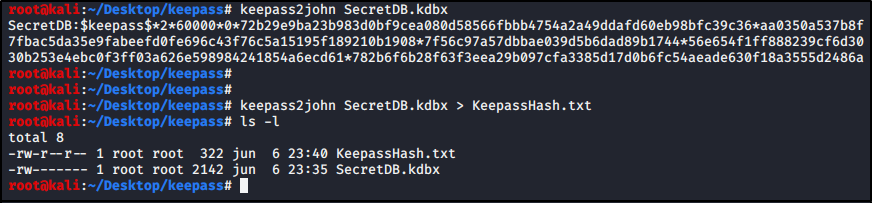
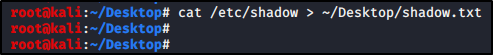
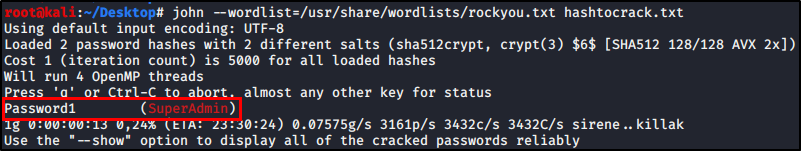
We now have our hash ready to be cracked. In this example we will try to crack it using a dictionary and John the ripper. I used a modified version of rockyou.txt as dictionary. You can also use other great cracking tools like hashcat but I went with john here.
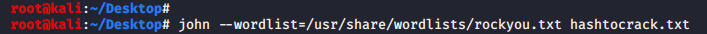
We run john and specify our custom wordlist with “–wordlist” parameter and then define our hash file. john --wordlist=rockyou.txt KeepassHash.txt
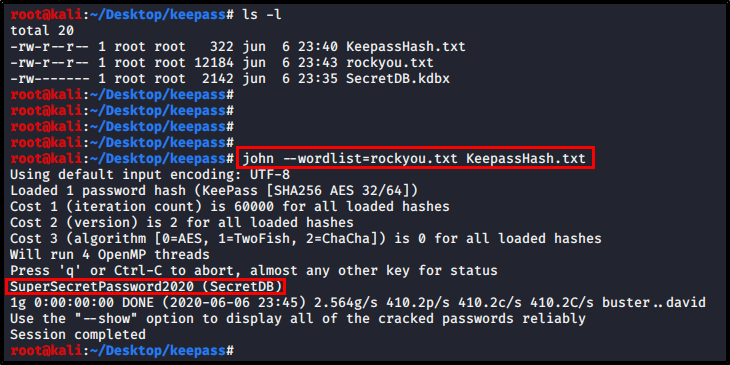
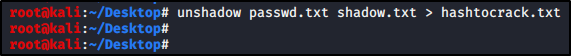
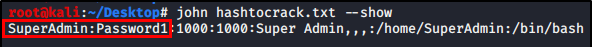
We then just let it run for some time and as soon as we crack the hash it will be displayed. As you can see in the screenshot we did crack the hash and the password of this SecretDB.kdbx-database was “SuperSecretPassword2020”.
I hope you found this post useful and make sure to not use weak password for your database.
// Rickard